UniVsThreats26 Quals中exe逆向Starfield Relay
CTF
一个复杂的exe程序逆向
描述 -- 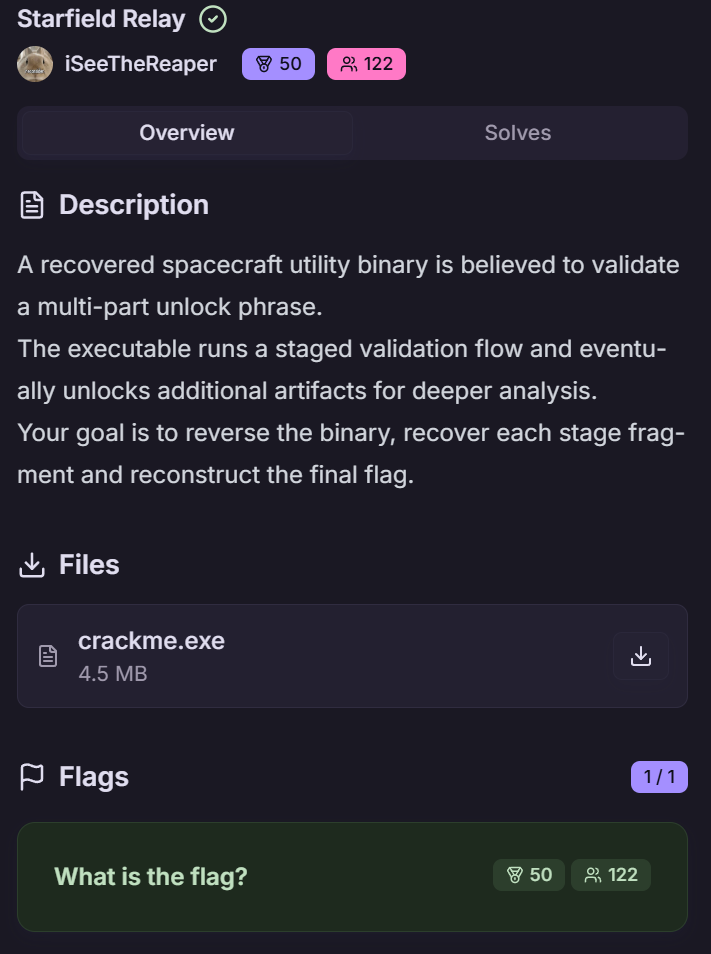 首先看到这里的描述就应该知道他有很多块去拼接成一个flag 一、程序整体结构 -------- 首先用die查看是否有壳顺便看看结构,就会得到一个无壳的exe程序,既然没有壳那就直接扔到ida去看看反编译后的代码就行 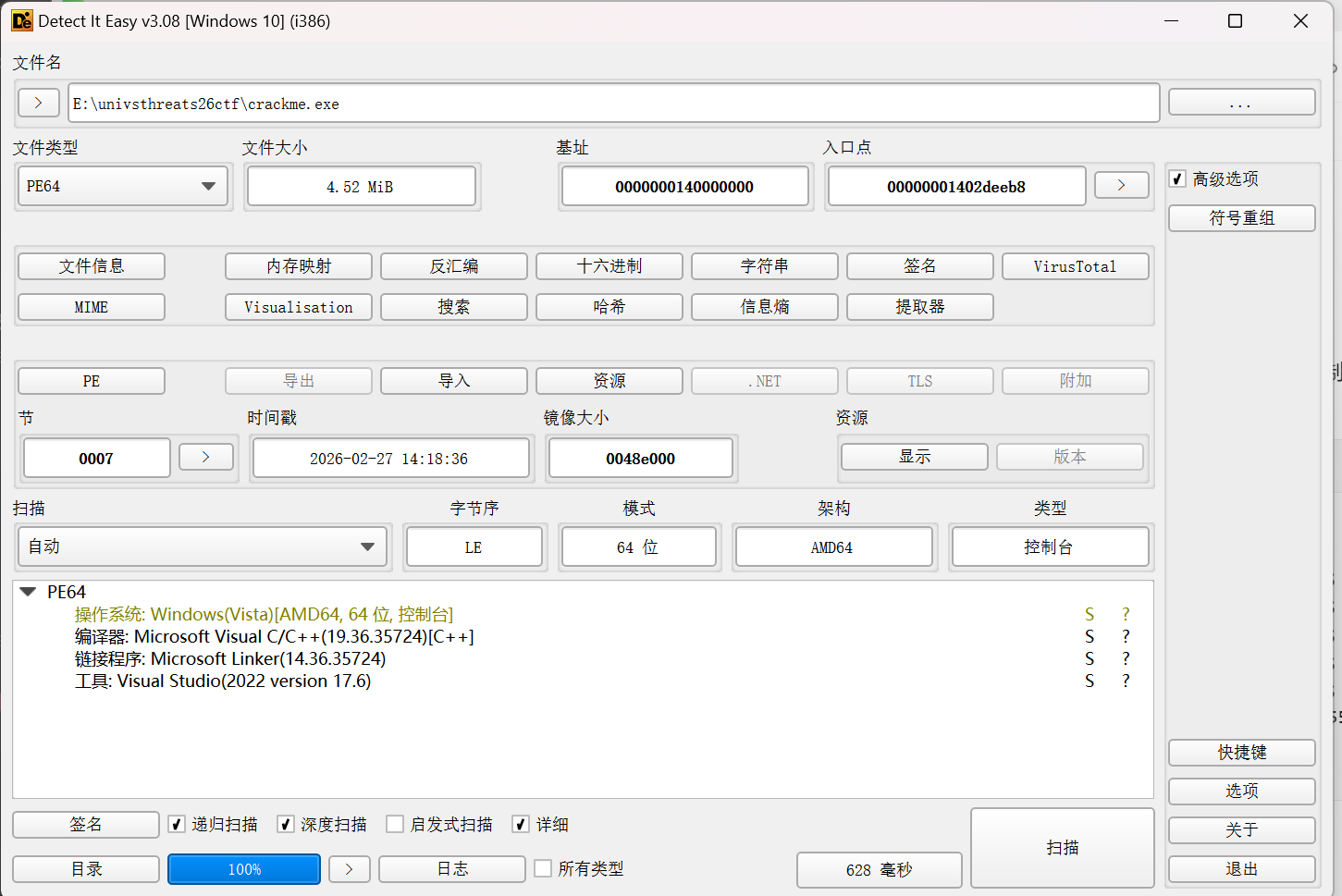 会逆向的都应该知道直接进去找main(入口)函数就行  完整代码如下: ```php int __fastcall main(int argc, const char **argv, const char **envp) { void *v3; // rax _QWORD *v4; // rax int n9; // r13d __m128i si128; // xmm6 __m128i v7; // xmm9 __m128i v8; // xmm8 __m128i v9; // xmm7 __m128i v10; // xmm10 __m128i v11; // xmm11 __m128i v12; // xmm12 char ZName; // bl signed int n32; // ecx signed int n4; // edx signed int n8; // r8d signed int n12; // r9d int i; // r8d signed int n32_1; // ecx signed int n4_1; // edx signed int n8_1; // r8d signed int n12_1; // r9d int j; // r8d signed int n32_2; // ecx signed int n4_2; // edx signed int n8_2; // r8d signed int n12_2; // r9d int k; // r8d signed int n32_3; // ecx signed int n4_3; // edx signed int n8_3; // r8d signed int n12_3; // r9d int m; // eax void *enter_fragment:__1; // rcx void **v119; // rdx size_t Size_1; // rdi void **Src_1; // r9 __int64 v122; // rsi void **v123; // rbx __int64 v124; // rax __int64 v125; // rax void *v126; // rcx void *v127; // rcx unsigned __int8 v128; // bl void *v129; // rcx void *v130; // rcx void **v131; // rdx __int64 v132; // rax void *v133; // rcx __m128i v135; // [rsp+30h] [rbp-1F8h] BYREF __m128i v136; // [rsp+40h] [rbp-1E8h] __m128i v137; // [rsp+50h] [rbp-1D8h] __m128i v138; // [rsp+60h] [rbp-1C8h] __m128i v139; // [rsp+70h] [rbp-1B8h] __m128i v140; // [rsp+80h] [rbp-1A8h] __m128i v141; // [rsp+90h] [rbp-198h] __m128i v142; // [rsp+A0h] [rbp-188h] __int128 enter_fragment:_; // [rsp+B0h] [rbp-178h] BYREF unsigned __int64 n16; // [rsp+C0h] [rbp-168h] unsigned __int64 n31; // [rsp+C8h] [rbp-160h] _BYTE v146[32]; // [rsp+D0h] [rbp-158h] BYREF void *Src[2]; // [rsp+F0h] [rbp-138h] BYREF size_t Size; // [rsp+100h] [rbp-128h] unsigned __int64 n15_1; // [rsp+108h] [rbp-120h] void *Block[2]; // [rsp+110h] [rbp-118h] BYREF __int64 v151; // [rsp+120h] [rbp-108h] unsigned __int64 n15_2; // [rsp+128h] [rbp-100h] void *v153[2]; // [rsp+130h] [rbp-F8h] BYREF __int64 v154; // [rsp+140h] [rbp-E8h] unsigned __int64 n15; // [rsp+148h] [rbp-E0h] _QWORD v156[4]; // [rsp+150h] [rbp-D8h] BYREF v135.m128i_i64[0] = (__int64)"uvt_crackme_work"; sub_14010CF90(v146); v3 = (void *)sub_140111FA0(Src); sub_14010FFC0(v156, v3); sub_140111980(Src); sub_140111980(v146); v135.m128i_i32[0] = 0; v135.m128i_i64[1] = (__int64)&off_140433020; sub_140111C90(v156, &v135); if ( v135.m128i_i32[0] ) sub_140111830("create_directories", &v135, v156); v135.m128i_i64[0] = (__int64)"progress.json"; v135.m128i_i64[1] = 13; sub_14010CF90(Block); v4 = (_QWORD *)sub_14010FFC0(&enter_fragment:_, v156); if ( v4[3] > 7u ) v4 = (_QWORD *)*v4; sub_1402DD7A4(v4); sub_140111980(&enter_fragment:_); sub_140111980(Block); *(_OWORD *)v153 = 0; v154 = 0; n15 = 15; LOBYTE(v153[0]) = 0; n9 = 0; sub_140113690(0, v156); si128 = _mm_load_si128((const __m128i *)&xmmword_14030D700); v7 = _mm_load_si128((const __m128i *)&xmmword_14030D780); v8 = _mm_load_si128((const __m128i *)&xmmword_14030D730); v9 = _mm_load_si128((const __m128i *)&xmmword_14030D710); v10 = _mm_load_si128((const __m128i *)&xmmword_14030D760); v11 = _mm_load_si128((const __m128i *)&xmmword_14030D750); v12 = _mm_load_si128((const __m128i *)&xmmword_14030D720); while ( 2 ) { *(_OWORD *)Src = 0; Size = 0; n15_1 = 15; LOBYTE(Src[0]) = 0; *(_OWORD *)Block = 0; v151 = 0; n15_2 = 15; LOBYTE(Block[0]) = 0; switch ( n9 ) { case 0: ZName = sub_1401156F0(Src, n6); goto LABEL_45; case 1: ZName = sub_140115860(Src, n6); goto LABEL_45; case 2: ZName = sub_140115B80(Src, n6); goto LABEL_45; case 3: ZName = sub_1401164A0(Src, n6); goto LABEL_45; case 4: ZName = sub_140117780(Src, n6); goto LABEL_45; case 5: ZName = sub_14011A330(v156); goto LABEL_45; case 6: *(_QWORD *)&enter_fragment:_ = 0x1337651AFE211D6CLL; *((_QWORD *)&enter_fragment:_ + 1) = 0xAFD493113C4616CDuLL; n16 = 0xACC4BDBB827002B5uLL; n31 = 0xA50D43D947FD5F9FuLL; if ( n6 < 6 ) { for ( i = 0; i < 32; ++i ) v146[i] = *((_BYTE *)&enter_fragment:_ + (unsigned int)i) ^ (17 * i + 9); } else { n32 = 0; v142 = v8; v141 = v12; v140 = v8; v139 = v12; v138 = v8; v137 = v12; v136 = v8; v135 = v12; n4 = 4; n8 = 8; n12 = 12; do { _XMM2 = _mm_cvtsi32_si128(v8.m128i_u32[0]); _XMM0 = _mm_shuffle_epi8(_mm_add_epi32(_mm_shuffle_epi32(_mm_cvtsi32_si128(n32), 0), v9), si128); __asm { vpmovzxbw ymm1, xmm0 vpmovzxbw ymm0, xmm2 vpmullw ymm1, ymm1, ymm0 vpmovwb xmm3, ymm1 } *(_DWORD *)&v146[n32] = _mm_cvtsi128_si32((__m128i)_mm_xor_ps( (__m128)_mm_add_epi8( _XMM3, _mm_cvtsi32_si128(v12.m128i_u32[0])), (__m128)_mm_cvtsi32_si128(*(_DWORD *)((char *)&enter_fragment:_ + (unsigned int)n32)))); _XMM0 = _mm_shuffle_epi8(_mm_add_epi32(_mm_shuffle_epi32(_mm_cvtsi32_si128(n4), 0), v9), si128); __asm { vpmovzxbw ymm1, xmm0 vpmovzxbw ymm0, xmm2 vpmullw ymm1, ymm1, ymm0 vpmovwb xmm3, ymm1 } *(_DWORD *)&v146[n4] = _mm_cvtsi128_si32((__m128i)_mm_xor_ps( (__m128)_mm_add_epi8( _XMM3, _mm_cvtsi32_si128(v12.m128i_u32[0])), (__m128)_mm_cvtsi32_si128(*(_DWORD *)((char *)&enter_fragment:_ + n4)))); _XMM0 = _mm_shuffle_epi8(_mm_add_epi32(_mm_shuffle_epi32(_mm_cvtsi32_si128(n8), 0), v9), si128); __asm { vpmovzxbw ymm1, xmm0 vpmovzxbw ymm0, xmm2 vpmullw ymm1, ymm1, ymm0 vpmovwb xmm3, ymm1 } *(_DWORD *)&v146[n8] = _mm_cvtsi128_si32((__m128i)_mm_xor_ps( (__m128)_mm_add_epi8( _XMM3, _mm_cvtsi32_si128(v12.m128i_u32[0])), (__m128)_mm_cvtsi32_si128(*(_DWORD *)((char *)&enter_fragment:_ + n8)))); _XMM0 = _mm_shuffle_epi8(_mm_add_epi32(_mm_shuffle_epi32(_mm_cvtsi32_si128(n12), 0), v9), si128); __asm { vpmovzxbw ymm1, xmm0 vpmovzxbw ymm0, xmm2 vpmullw ymm1, ymm1, ymm0 vpmovwb xmm3, ymm1 } *(_DWORD *)&v146[n12] = _mm_cvtsi128_si32((__m128i)_mm_xor_ps( (__m128)_mm_add_epi8( _XMM3, _mm_cvtsi32_si128(v12.m128i_u32[0])), (__m128)_mm_cvtsi32_si128(*(_DWORD *)((char *)&enter_fragment:_ + n12)))); n32 += 16; n4 += 16; n8 += 16; n12 += 16; } while ( n32 < 32 ); } goto LABEL_18; case 7: *(_QWORD *)&enter_fragment:_ = 0x559D8797A3CD04E3LL; *((_QWORD *)&enter_fragment:_ + 1) = 0xA7E2BC58A5629BBEuLL; n16 = 0xD69016B4DCE1DA00uLL; n31 = 0xB3CB0A1C4E40E0A0uLL; if ( n6 < 6 ) { for ( j = 0; j < 32; ++j ) v146[j] = *((_BYTE *)&enter_fragment:_ + (unsigned int)j) ^ (17 * j + 38); } else { n32_1 = 0; v135 = v8; v136 = v11; v137 = v8; v138 = v11; v139 = v8; v140 = v11; v141 = v8; v142 = v11; n4_1 = 4; n8_1 = 8; n12_1 = 12; do { _XMM2 = _mm_cvtsi32_si128(v8.m128i_u32[0]); _XMM0 = _mm_shuffle_epi8(_mm_add_epi32(_mm_shuffle_epi32(_mm_cvtsi32_si128(n32_1), 0), v9), si128); __asm { vpmovzxbw ymm1, xmm0 vpmovzxbw ymm0, xmm2 vpmullw ymm1, ymm1, ymm0 vpmovwb xmm3, ymm1 } *(_DWORD *)&v146[n32_1] = _mm_cvtsi128_si32((__m128i)_mm_xor_ps( (__m128)_mm_add_epi8( _XMM3, _mm_cvtsi32_si128(v11.m128i_u32[0])), (__m128)_mm_cvtsi32_si128(*(_DWORD *)((char *)&enter_fragment:_ + (unsigned int)n32_1)))); _XMM0 = _mm_shuffle_epi8(_mm_add_epi32(_mm_shuffle_epi32(_mm_cvtsi32_si128(n4_1), 0), v9), si128); __asm { vpmovzxbw ymm1, xmm0 vpmovzxbw ymm0, xmm2 vpmullw ymm1, ymm1, ymm0 vpmovwb xmm3, ymm1 } *(_DWORD *)&v146[n4_1] = _mm_cvtsi128_si32((__m128i)_mm_xor_ps( (__m128)_mm_add_epi8( _XMM3, _mm_cvtsi32_si128(v11.m128i_u32[0])), (__m128)_mm_cvtsi32_si128(*(_DWORD *)((char *)&enter_fragment:_ + n4_1)))); _XMM0 = _mm_shuffle_epi8(_mm_add_epi32(_mm_shuffle_epi32(_mm_cvtsi32_si128(n8_1), 0), v9), si128); __asm { vpmovzxbw ymm1, xmm0 vpmovzxbw ymm0, xmm2 vpmullw ymm1, ymm1, ymm0 vpmovwb xmm3, ymm1 } *(_DWORD *)&v146[n8_1] = _mm_cvtsi128_si32((__m128i)_mm_xor_ps( (__m128)_mm_add_epi8( _XMM3, _mm_cvtsi32_si128(v11.m128i_u32[0])), (__m128)_mm_cvtsi32_si128(*(_DWORD *)((char *)&enter_fragment:_ + n8_1)))); _XMM0 = _mm_shuffle_epi8(_mm_add_epi32(_mm_shuffle_epi32(_mm_cvtsi32_si128(n12_1), 0), v9), si128); __asm { vpmovzxbw ymm1, xmm0 vpmovzxbw ymm0, xmm2 vpmullw ymm1, ymm1, ymm0 vpmovwb xmm3, ymm1 } *(_DWORD *)&v146[n12_1] = _mm_cvtsi128_si32((__m128i)_mm_xor_ps( (__m128)_mm_add_epi8( _XMM3, _mm_cvtsi32_si128(v11.m128i_u32[0])), (__m128)_mm_cvtsi32_si128(*(_DWORD *)((char *)&enter_fragment:_ + n12_1)))); n32_1 += 16; n4_1 += 16; n8_1 += 16; n12_1 += 16; } while ( n32_1 < 32 ); } LABEL_18: enter_fragment:_ = 0; n16 = 0; n31 = 0; *(_QWORD *)&enter_fragment:_ = operator new(0x20u); n16 = 16; n31 = 31; strcpy((char *)enter_fragment:_, "enter fragment: "); ZName = UnDecorator::getZName(&enter_fragment:_, 15, v146, Src); goto LABEL_40; case 8: *(_QWORD *)&enter_fragment:_ = 0x6631BB9C2E715E3ELL; *((_QWORD *)&enter_fragment:_ + 1) = 0xF7A6B7BB6932B56FuLL; n16 = 0x2FA266079B0A930ELL; n31 = 0x8C63030328BE53BCuLL; if ( n6 < 6 ) { for ( k = 0; k < 32; ++k ) v146[k] = *((_BYTE *)&enter_fragment:_ + (unsigned int)k) ^ (17 * k + 67); } else { n32_2 = 0; v135 = v8; v136 = v10; v137 = v8; v138 = v10; v139 = v8; v140 = v10; v141 = v8; v142 = v10; n4_2 = 4; n8_2 = 8; n12_2 = 12; do { _XMM2 = _mm_cvtsi32_si128(v8.m128i_u32[0]); _XMM0 = _mm_shuffle_epi8(_mm_add_epi32(_mm_shuffle_epi32(_mm_cvtsi32_si128(n32_2), 0), v9), si128); __asm { vpmovzxbw ymm1, xmm0 vpmovzxbw ymm0, xmm2 vpmullw ymm1, ymm1, ymm0 vpmovwb xmm3, ymm1 } *(_DWORD *)&v146[n32_2] = _mm_cvtsi128_si32((__m128i)_mm_xor_ps( (__m128)_mm_add_epi8( _XMM3, _mm_cvtsi32_si128(v10.m128i_u32[0])), (__m128)_mm_cvtsi32_si128(*(_DWORD *)((char *)&enter_fragment:_ + (unsigned int)n32_2)))); _XMM0 = _mm_shuffle_epi8(_mm_add_epi32(_mm_shuffle_epi32(_mm_cvtsi32_si128(n4_2), 0), v9), si128); __asm { vpmovzxbw ymm1, xmm0 vpmovzxbw ymm0, xmm2 vpmullw ymm1, ymm1, ymm0 vpmovwb xmm3, ymm1 } *(_DWORD *)&v146[n4_2] = _mm_cvtsi128_si32((__m128i)_mm_xor_ps( (__m128)_mm_add_epi8( _XMM3, _mm_cvtsi32_si128(v10.m128i_u32[0])), (__m128)_mm_cvtsi32_si128(*(_DWORD *)((char *)&enter_fragment:_ + n4_2)))); _XMM0 = _mm_shuffle_epi8(_mm_add_epi32(_mm_shuffle_epi32(_mm_cvtsi32_si128(n8_2), 0), v9), si128); __asm { vpmovzxbw ymm1, xmm0 vpmovzxbw ymm0, xmm2 vpmullw ymm1, ymm1, ymm0 vpmovwb xmm3, ymm1 } *(_DWORD *)&v146[n8_2] = _mm_cvtsi128_si32((__m128i)_mm_xor_ps( (__m128)_mm_add_epi8( _XMM3, _mm_cvtsi32_si128(v10.m128i_u32[0])), (__m128)_mm_cvtsi32_si128(*(_DWORD *)((char *)&enter_fragment:_ + n8_2)))); _XMM0 = _mm_shuffle_epi8(_mm_add_epi32(_mm_shuffle_epi32(_mm_cvtsi32_si128(n12_2), 0), v9), si128); __asm { vpmovzxbw ymm1, xmm0 vpmovzxbw ymm0, xmm2 vpmullw ymm1, ymm1, ymm0 vpmovwb xmm3, ymm1 } *(_DWORD *)&v146[n12_2] = _mm_cvtsi128_si32((__m128i)_mm_xor_ps( (__m128)_mm_add_epi8( _XMM3, _mm_cvtsi32_si128(v10.m128i_u32[0])), (__m128)_mm_cvtsi32_si128(*(_DWORD *)((char *)&enter_fragment:_ + n12_2)))); n32_2 += 16; n4_2 += 16; n8_2 += 16; n12_2 += 16; } while ( n32_2 < 32 ); } enter_fragment:_ = 0; n16 = 0; n31 = 0; *(_QWORD *)&enter_fragment:_ = operator new(0x20u); n16 = 16; n31 = 31; strcpy((char *)enter_fragment:_, "enter fragment: "); ZName = UnDecorator::getZName(&enter_fragment:_, 8, v146, Src); goto LABEL_40; case 9: *(_QWORD *)&enter_fragment:_ = 0x9BCA8E41DA194AC4uLL; *((_QWORD *)&enter_fragment:_ + 1) = 0x472C127403C3A31CLL; n16 = 0xE65CB35E474AFBFFuLL; n31 = 0xB4FA7B6500038971uLL; if ( n6 < 6 ) { for ( m = 0; m < 32; ++m ) v146[m] = *((_BYTE *)&enter_fragment:_ + (unsigned int)m) ^ (17 * m + 96); } else { n32_3 = 0; v135 = v8; v136 = v7; v137 = v8; v138 = v7; v139 = v8; v140 = v7; v141 = v8; v142 = v7; n4_3 = 4; n8_3 = 8; n12_3 = 12; do { _XMM2 = _mm_cvtsi32_si128(v8.m128i_u32[0]); _XMM0 = _mm_shuffle_epi8(_mm_add_epi32(_mm_shuffle_epi32(_mm_cvtsi32_si128(n32_3), 0), v9), si128); __asm { vpmovzxbw ymm1, xmm0 vpmovzxbw ymm0, xmm2 vpmullw ymm1, ymm1, ymm0 vpmovwb xmm3, ymm1 } *(_DWORD *)&v146[n32_3] = _mm_cvtsi128_si32((__m128i)_mm_xor_ps( (__m128)_mm_add_epi8( _XMM3, _mm_cvtsi32_si128(v7.m128i_u32[0])), (__m128)_mm_cvtsi32_si128(*(_DWORD *)((char *)&enter_fragment:_ + (unsigned int)n32_3)))); _XMM0 = _mm_shuffle_epi8(_mm_add_epi32(_mm_shuffle_epi32(_mm_cvtsi32_si128(n4_3), 0), v9), si128); __asm { vpmovzxbw ymm1, xmm0 vpmovzxbw ymm0, xmm2 vpmullw ymm1, ymm1, ymm0 vpmovwb xmm3, ymm1 } *(_DWORD *)&v146[n4_3] = _mm_cvtsi128_si32((__m128i)_mm_xor_ps( (__m128)_mm_add_epi8( _XMM3, _mm_cvtsi32_si128(v7.m128i_u32[0])), (__m128)_mm_cvtsi32_si128(*(_DWORD *)((char *)&enter_fragment:_ + n4_3)))); _XMM0 = _mm_shuffle_epi8(_mm_add_epi32(_mm_shuffle_epi32(_mm_cvtsi32_si128(n8_3), 0), v9), si128); __asm { vpmovzxbw ymm1, xmm0 vpmovzxbw ymm0, xmm2 vpmullw ymm1, ymm1, ymm0 vpmovwb xmm3, ymm1 } *(_DWORD *)&v146[n8_3] = _mm_cvtsi128_si32((__m128i)_mm_xor_ps( (__m128)_mm_add_epi8( _XMM3, _mm_cvtsi32_si128(v7.m128i_u32[0])), (__m128)_mm_cvtsi32_si128(*(_DWORD *)((char *)&enter_fragment:_ + n8_3)))); _XMM0 = _mm_shuffle_epi8(_mm_add_epi32(_mm_shuffle_epi32(_mm_cvtsi32_si128(n12_3), 0), v9), si128); __asm { vpmovzxbw ymm1, xmm0 vpmovzxbw ymm0, xmm2 vpmullw ymm1, ymm1, ymm0 vpmovwb xmm3, ymm1 } *(_DWORD *)&v146[n12_3] = _mm_cvtsi128_si32((__m128i)_mm_xor_ps( (__m128)_mm_add_epi8( _XMM3, _mm_cvtsi32_si128(v7.m128i_u32[0])), (__m128)_mm_cvtsi32_si128(*(_DWORD *)((char *)&enter_fragment:_ + n12_3)))); n32_3 += 16; n4_3 += 16; n8_3 += 16; n12_3 += 16; } while ( n32_3 < 32 ); } enter_fragment:_ = 0; n16 = 0; n31 = 0; *(_QWORD *)&enter_fragment:_ = operator new(0x20u); n16 = 16; n31 = 31; strcpy((char *)enter_fragment:_, "enter fragment: "); ZName = UnDecorator::getZName(&enter_fragment:_, 7, v146, Src); LABEL_40: if ( n31 > 0xF ) { enter_fragment:__1 = (void *)enter_fragment:_; if ( n31 + 1 >= 0x1000 ) { if ( (unsigned __int64)(enter_fragment:_ - *(_QWORD *)(enter_fragment:_ - 8) - 8) > 0x1F ) __fastfail(5u); enter_fragment:__1 = *(void **)(enter_fragment:_ - 8); } j_j_j__free_base(enter_fragment:__1); } LABEL_45: if ( v151 ) { v119 = Block; if ( n15_2 > 0xF ) v119 = (void **)Block[0]; sub_14010D820(&qword_14043A5E0, v119); } if ( !ZName ) goto LABEL_72; Size_1 = Size; Src_1 = Src; if ( n15_1 > 0xF ) Src_1 = (void **)Src[0]; v122 = v154; if ( Size > n15 - v154 ) { sub_14010DF60(v153, Size); } else { v154 += Size; v123 = v153; if ( n15 > 0xF ) v123 = (void **)v153[0]; memcpy((char *)v123 + v122, Src_1, Size); *((_BYTE *)v123 + Size_1 + v122) = 0; } v124 = sub_14010C790(&qword_14043A5E0, "Great! Stage "); v125 = sub_14010FC90(v124, (unsigned int)++n9); sub_14010C790(v125, "/10 done.\n"); if ( n9 <= 9 ) { sub_14010C790(&qword_14043A5E0, "\n"); sub_14010C790(&qword_14043A5E0, "Next:\n"); sub_140113690(n9, v156); } if ( n15_2 <= 0xF ) goto LABEL_64; v126 = Block[0]; if ( n15_2 + 1 < 0x1000 ) goto LABEL_63; if ( (unsigned __int64)Block[0] - *((_QWORD *)Block[0] - 1) - 8 > 0x1F ) goto LABEL_75; v126 = (void *)*((_QWORD *)Block[0] - 1); LABEL_63: j_j_j__free_base(v126); LABEL_64: v151 = 0; n15_2 = 15; LOBYTE(Block[0]) = 0; if ( n15_1 <= 0xF ) goto LABEL_69; v127 = Src[0]; if ( n15_1 + 1 < 0x1000 ) goto LABEL_68; if ( (unsigned __int64)Src[0] - *((_QWORD *)Src[0] - 1) - 8 > 0x1F ) goto LABEL_81; v127 = (void *)*((_QWORD *)Src[0] - 1); LABEL_68: j_j_j__free_base(v127); LABEL_69: if ( n9 <= 9 ) continue; v128 = 0; LABEL_85: v131 = v153; if ( n15 > 0xF ) v131 = (void **)v153[0]; v132 = sub_14010D820(&qword_14043A4C0, v131); sub_14010C790(v132, "\n"); if ( n15 > 0xF ) { if ( n15 + 1 < 0x1000 ) { v133 = v153[0]; } else { v133 = (void *)*((_QWORD *)v153[0] - 1); if ( (unsigned __int64)((char *)v153[0] - (char *)v133 - 8) > 0x1F ) __fastfail(5u); } j_j_j__free_base(v133); } v154 = 0; n15 = 15; LOBYTE(v153[0]) = 0; sub_140111980(v156); return v128; default: LABEL_72: sub_14010C790(&qword_14043A5E0, "stage failed\n"); if ( n15_2 <= 0xF ) goto LABEL_78; if ( n15_2 + 1 < 0x1000 ) { v129 = Block[0]; } else { v129 = (void *)*((_QWORD *)Block[0] - 1); if ( (unsigned __int64)((char *)Block[0] - (char *)v129 - 8) > 0x1F ) LABEL_75: __fastfail(5u); } j_j_j__free_base(v129); LABEL_78: v151 = 0; n15_2 = 15; LOBYTE(Block[0]) = 0; if ( n15_1 <= 0xF ) goto LABEL_84; if ( n15_1 + 1 < 0x1000 ) { v130 = Src[0]; } else { v130 = (void *)*((_QWORD *)Src[0] - 1); if ( (unsigned __int64)((char *)Src[0] - (char *)v130 - 8) > 0x1F ) LABEL_81: __fastfail(5u); } j_j_j__free_base(v130); LABEL_84: v128 = 1; goto LABEL_85; } } } ``` 用cmd打开exe文件就会看到需要输入10个片段才行 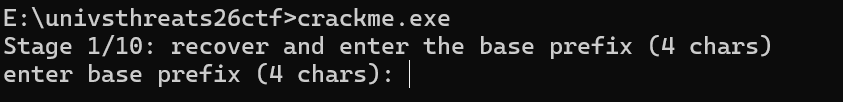 程序是一个10阶段的crackme,每个阶段通过`n9`变量控制流程。主函数`main`中的switch语句分发到各个阶段函数。 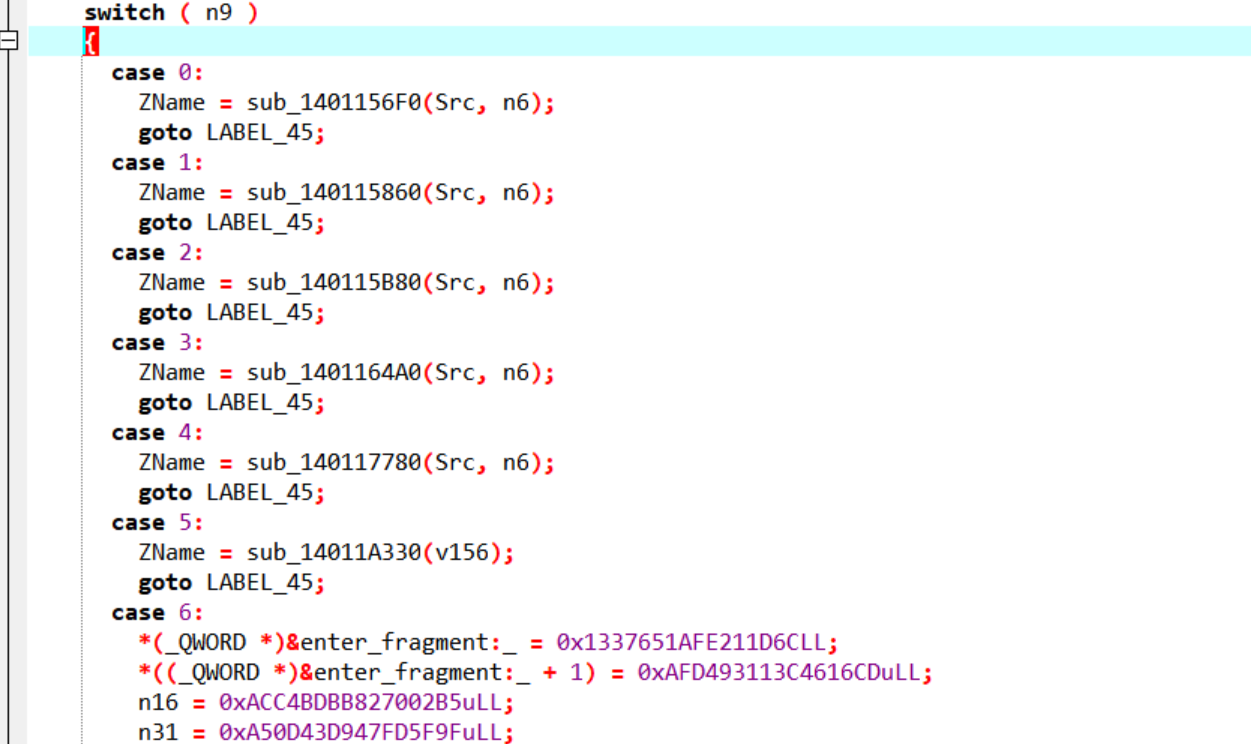 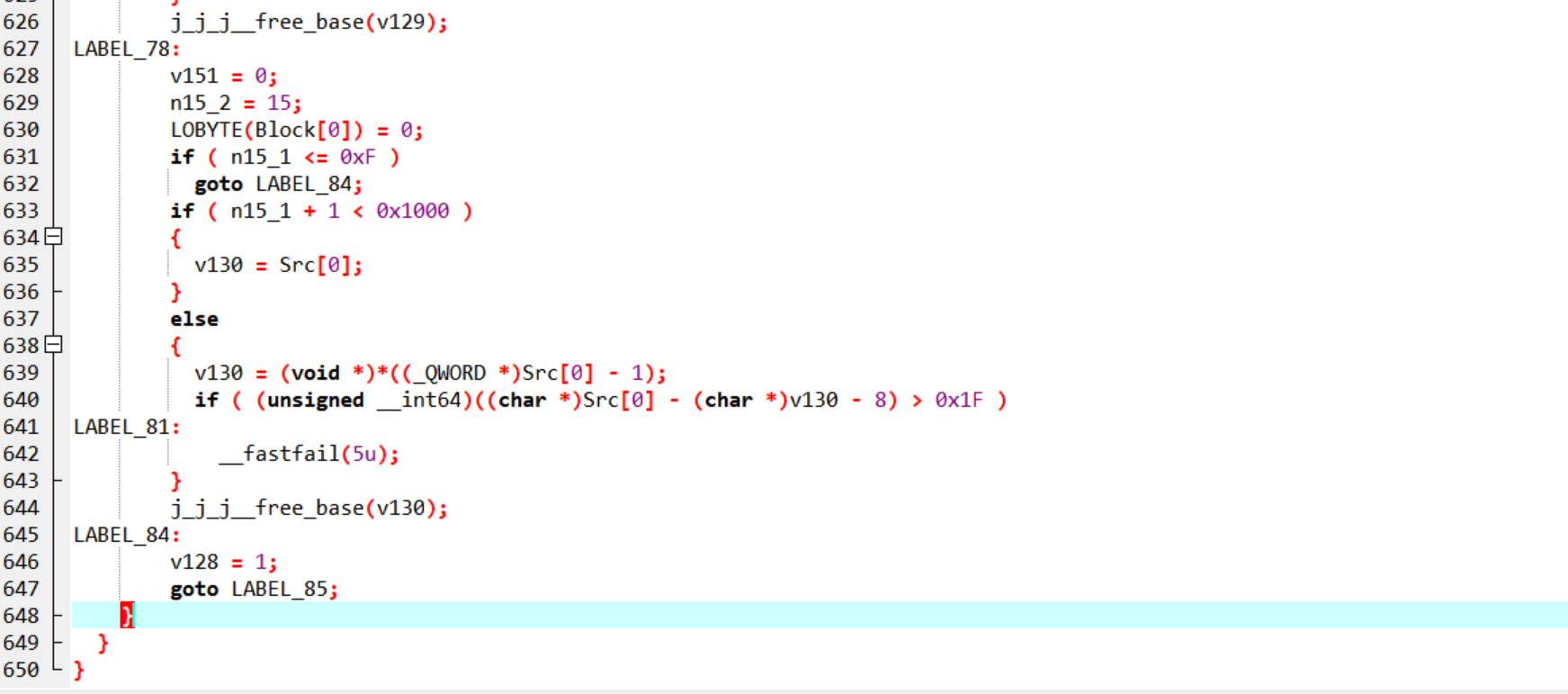 ```php switch ( n9 ) { case 0: ZName = sub_1401156F0(Src, n6); goto LABEL_45; case 1: ZName = sub_140115860(Src, n6); goto LABEL_45; case 2: ZName = sub_140115B80(Src, n6); goto LABEL_45; case 3: ZName = sub_1401164A0(Src, n6); goto LABEL_45; case 4: ZName = sub_140117780(Src, n6); goto LABEL_45; case 5: ZName = sub_14011A330(v156); goto LABEL_45; // ... 阶段6-9是哈希验证 if ( n15_1 + 1 < 0x1000 ) { v130 = Src[0]; } else { v130 = (void *)*((_QWORD *)Src[0] - 1); if ( (unsigned __int64)((char *)Src[0] - (char *)v130 - 8) > 0x1F ) LABEL_81: __fastfail(5u); } j_j_j__free_base(v130); LABEL_84: v128 = 1; goto LABEL_85; } ``` 二、各阶段详细分析 --------- ### 阶段0->Stage1 (`sub_1401156F0`) **函数位置**:`sub_1401156F0` ```php if ( !Src ) return 0; *(_OWORD *)Buf1 = 0; Size = 0; n15 = 15; LOBYTE(Buf1[0]) = 0; sub_14010C790(&qword_14043A5E0, "enter base prefix (4 chars): "); v4 = *(_QWORD *)(*(__int64 *)((char *)&qword_14043A430[8] + *(int *)(qword_14043A430[0] + 4)) + 8); v15 = v4; (*(void (__fastcall **)(__int64))(*(_QWORD *)v4 + 8LL))(v4); v5 = sub_14010EA10(v14); LOBYTE(v6) = 10; v7 = (*(__int64 (__fastcall **)(__int64, __int64))(*(_QWORD *)v5 + 64LL))(v5, v6); v8 = (void (__fastcall ***)(_QWORD, __int64))(*(__int64 (__fastcall **)(__int64))(*(_QWORD *)v4 + 16LL))(v4); if ( v8 ) (**v8)(v8, 1); sub_14010E7A0(qword_14043A430, Buf1, v7); n15_1 = n15; Buf1_1 = Buf1; v11 = Buf1[0]; if ( n15 > 0xF ) Buf1_1 = (void **)Buf1[0]; if ( Size == 4 && !memcmp(Buf1_1, "UVT{", 4u) ) { sub_14010CB90(Src, "UVT{", 4); v12 = 1; } else { v12 = 0; } if ( n15_1 > 0xF ) { if ( n15_1 + 1 < 0x1000 ) { v13 = v11; } else { v13 = (_BYTE *)*((_QWORD *)v11 - 1); if ( (unsigned __int64)(v11 - v13 - 8) > 0x1F ) __fastfail(5u); } j_j_j__free_base(v13); } return v12; } ``` **关键代码**: ```php if ( Size == 4 && !memcmp(Buf1_1, "UVT{", 4u) ) { sub_14010CB90(Src, "UVT{", 4); return 1; } ``` **数据来源**:直接硬编码字符串 `"UVT{"` 所以直接输入UVT{就可以 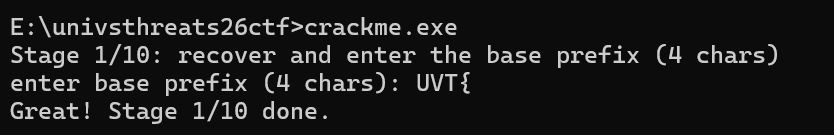 - - - - - - ### 阶段1->Stage2(`sub_140115860` + `sub_140115AA0`) **函数位置:**`**sub_140115860**` ```php if ( !Src ) return 0; *(_OWORD *)Buf1 = 0; n3 = 0; n15 = 15; LOBYTE(Buf1[0]) = 0; sub_14010C790(&qword_14043A5E0, "enter fragment (3 chars): "); v4 = *(_QWORD *)(*(__int64 *)((char *)&qword_14043A430[8] + *(int *)(qword_14043A430[0] + 4)) + 8); v23 = v4; (*(void (__fastcall **)(__int64))(*(_QWORD *)v4 + 8LL))(v4); v5 = sub_14010EA10(v22); LOBYTE(v6) = 10; v7 = (*(__int64 (__fastcall **)(__int64, __int64))(*(_QWORD *)v5 + 64LL))(v5, v6); v8 = (void (__fastcall ***)(_QWORD, __int64))(*(__int64 (__fastcall **)(__int64))(*(_QWORD *)v4 + 16LL))(v4); if ( v8 ) (**v8)(v8, 1); sub_14010E7A0(qword_14043A430, Buf1, v7); n15_1 = n15; Buf1_2 = (void **)Buf1[0]; if ( n3 == 3 ) { sub_140115AA0(Src_1); Buf1_1 = Buf1; if ( n15_1 > 0xF ) Buf1_1 = Buf1_2; n0xF_1 = n0xF; Src_2 = Src_1; v15 = Src_1[0]; if ( n0xF > 0xF ) Src_2 = (void **)Src_1[0]; if ( *(_BYTE *)Buf1_1 != *(_BYTE *)Src_2 ) goto LABEL_27; Buf1_3 = Buf1; if ( n15_1 > 0xF ) Buf1_3 = Buf1_2; Src_3 = Src_1; if ( n0xF > 0xF ) Src_3 = (void **)Src_1[0]; if ( *((_BYTE *)Buf1_3 + 1) != *((_BYTE *)Src_3 + 1) ) goto LABEL_27; Buf1_4 = Buf1; if ( n15_1 > 0xF ) Buf1_4 = Buf1_2; Src_4 = Src_1; if ( n0xF > 0xF ) Src_4 = (void **)Src_1[0]; if ( *((_BYTE *)Buf1_4 + 2) == *((_BYTE *)Src_4 + 2) ) { if ( Src != Src_1 ) { Src_5 = Src_1; if ( n0xF > 0xF ) Src_5 = (void **)Src_1[0]; sub_14010CB90(Src, Src_5, Size); n0xF_1 = n0xF; v15 = Src_1[0]; } v11 = 1; } else { LABEL_27: v11 = 0; } if ( n0xF_1 > 0xF ) { if ( n0xF_1 + 1 >= 0x1000 ) { if ( (unsigned __int64)v15 - *(v15 - 1) - 8 > 0x1F ) __fastfail(5u); v15 = (_QWORD *)*(v15 - 1); } j_j_j__free_base(v15); } Size = 0; n0xF = 15; LOBYTE(Src_1[0]) = 0; } else { v11 = 0; } if ( n15_1 > 0xF ) { if ( n15_1 + 1 < 0x1000 ) { Buf1_5 = Buf1_2; } else { Buf1_5 = (void **)*(Buf1_2 - 1); if ( (unsigned __int64)((char *)Buf1_2 - (char *)Buf1_5 - 8) > 0x1F ) __fastfail(5u); } j_j_j__free_base(Buf1_5); } return v11; } ``` 这里和阶段1一样都是比对数据,那这里的比对数据并不在外面 **关键逻辑:** ```php n15_1 = n15; Buf1_2 = (void **)Buf1[0]; if ( n3 == 3 ) { sub_140115AA0(Src_1); ``` 这里直接初始化了src\_1也就是说这里面也有可能是硬编码我们不确定继续往下看逻辑 ```php Buf1_1 = Buf1; if ( n15_1 > 0xF ) Buf1_1 = Buf1_2; n0xF_1 = n0xF; Src_2 = Src_1; v15 = Src_1[0]; if ( n0xF > 0xF ) Src_2 = (void **)Src_1[0]; if ( *(_BYTE *)Buf1_1 != *(_BYTE *)Src_2 ) goto LABEL_27; Buf1_3 = Buf1; if ( n15_1 > 0xF ) Buf1_3 = Buf1_2; Src_3 = Src_1; if ( n0xF > 0xF ) Src_3 = (void **)Src_1[0]; if ( *((_BYTE *)Buf1_3 + 1) != *((_BYTE *)Src_3 + 1) ) goto LABEL_27; Buf1_4 = Buf1; if ( n15_1 > 0xF ) Buf1_4 = Buf1_2; Src_4 = Src_1; if ( n0xF > 0xF ) Src_4 = (void **)Src_1[0]; if ( *((_BYTE *)Buf1_4 + 2) == *((_BYTE *)Src_4 + 2) ) ``` 看完了这里就会发现这是从140115AA0函数出来的数据与你输入的数据进行比对,那主要的数据就在这个函数里 **函数位置:**`**sub_140115AA0**` **硬编码位置** ```php void **__fastcall sub_140115AA0(void **Src) { void **Src_1; // rax void **Src_2; // rcx Src_1 = Src; *(_OWORD *)Src = 0; Src[3] = (void *)15; *(_BYTE *)Src = 0; Src[2] = (void *)3; *(_DWORD *)Src = 0; if ( (unsigned __int64)Src[3] > 0xF ) Src = (void **)*Src; *(_BYTE *)Src = 75; if ( (unsigned __int64)Src_1[3] <= 0xF ) Src_2 = Src_1; else Src_2 = (void **)*Src_1; *((_BYTE *)Src_2 + 1) = 114; if ( (unsigned __int64)Src_1[3] <= 0xF ) *((_BYTE *)Src_1 + 2) = 52; else *((_BYTE *)*Src_1 + 2) = 52; return Src_1; } ``` **关键代码**: ```php *(_BYTE *)Src = 75; // 'K' *((_BYTE *)Src_2 + 1) = 114; // 'r' *((_BYTE *)Src_1 + 2) = 52; // '4' ``` 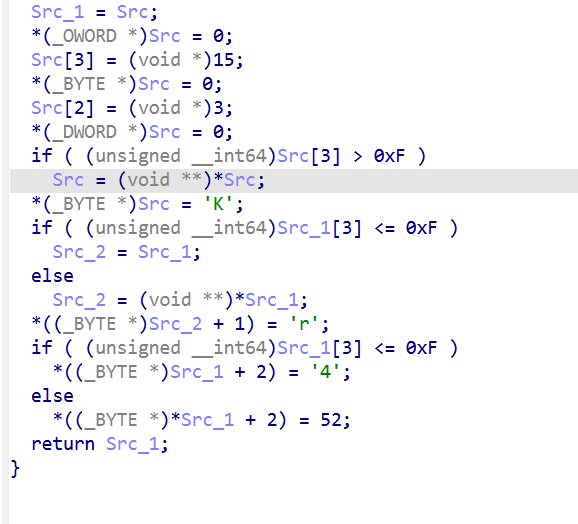 因为他这里就说了长度是3所以直接输入Kr4就可以 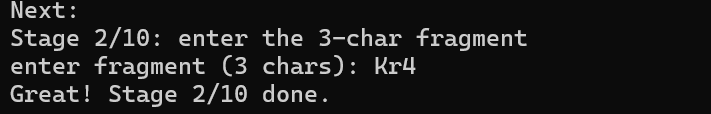 - - - - - - ### 阶段2->Stage3 (`sub_140115B80`) **函数位置**:`sub_140115B80` 代码很长就只挑出来关键代码与关键逻辑 **关键代码**: ```php *(_QWORD *)&v51[0] = 0xC5E42C25FADC2431ui64; for ( i = 0i64; i < 8; ++i ) { if ( 7 * (_BYTE)i + (*((_BYTE *)v11 + i) ^ (unsigned __int8)(17 * i + 109)) + 19 != *((_BYTE *)v51 + i) ) goto LABEL_93; } ``` 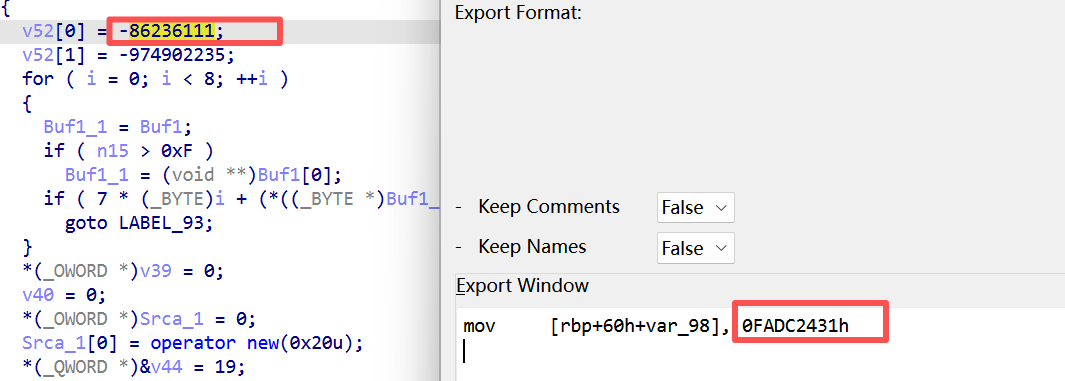 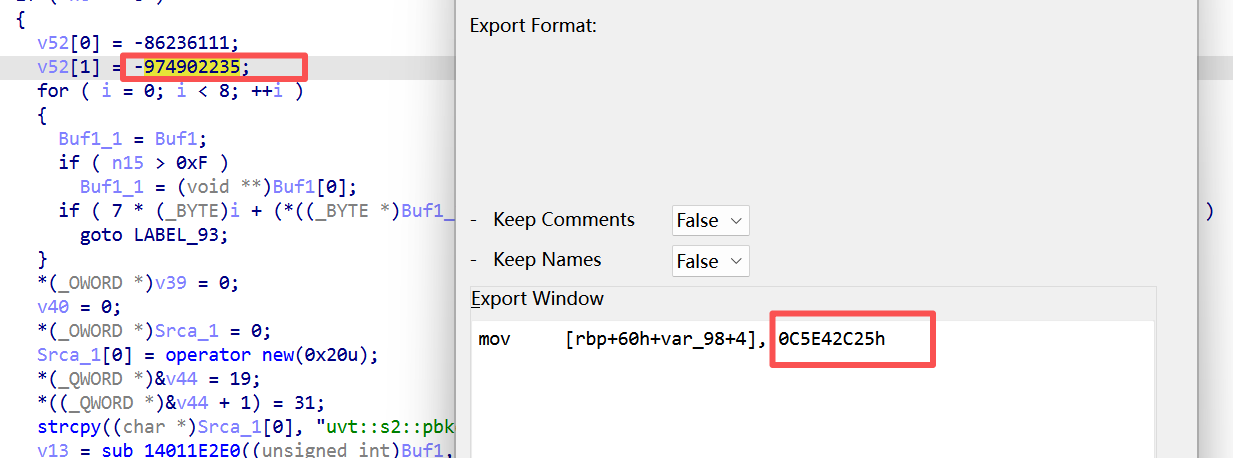 `0xC5E42C25FADC2431` 是一个64位整数,小端序展开为8字节: `0xC5E42C25FADC2431` 小端序 → `[0x31, 0x24, 0xDC, 0xFA, 0x25, 0x2C, 0xE4, 0xC5]` **关键逻辑**: `7*i + (input[i] ^ (17*i + 109)) + 19 = target[i]` **解密脚本**: ```php def solve_stage2(): # 从 0xC5E42C25FADC2431 小端序得到 target_bytes = [0x31, 0x24, 0xDC, 0xFA, 0x25, 0x2C, 0xE4, 0xC5] result = [] for i in range(8): mask = (17 * i + 109) & 0xFF val = (target_bytes[i] - 19 - 7 * i) & 0xFF result.append(val ^ mask) token = bytes(result).decode('ascii') print(f"Stage 2 token: {token}") # st4rG4te return token ``` 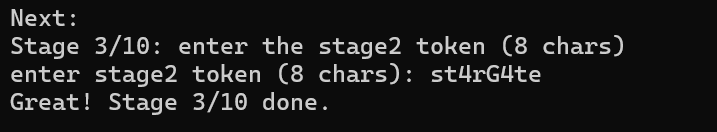 - - - - - - ### 阶段3->Stage4 (`sub_1401164A0`) **函数位置**:`sub_1401164A0` 中第一层验证 **关键代码**: ```php v36[0] = -307768873; // 0xEDA7D1D7 v36[1] = 1231567188; // 0x49683954 for ( i = 0i64; i < 8; ++i ) { if ( 3 * (_BYTE)i + (*((_BYTE *)v7 + i) ^ (unsigned __int8)(-89 - 11 * i)) != *((_BYTE *)v36 + i) ) goto LABEL_98; } ``` 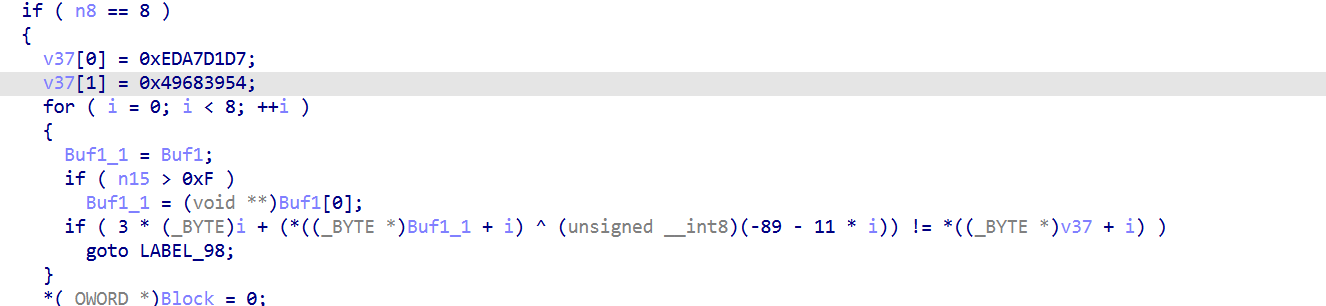 **数据来源**:两个32位整数,小端序展开: - `0xEDA7D1D7` → `[0xD7, 0xD1, 0xA7, 0xED]` - `0x49683954` → `[0x54, 0x39, 0x68, 0x49]` **验证方程**: `3*i + (input[i] ^ (-89 - 11*i)) = target[i]` **解密脚本**: ```php def solve_stage3(): # 实际运行时的 target 值 target_bytes = [0xD7, 0xD1, 0xA7, 0xED, 0x54, 0x39, 0x68, 0x49] result = [] for i in range(8): mask = (-89 - 11 * i) & 0xFF val = (target_bytes[i] - 3 * i) & 0xFF result.append(val ^ mask) token = bytes(result).decode('ascii') print(f"Stage 3 token: {token}") # pR0b3Z3n return token ``` 注意,但为什么下面还有那么长数据,只写这一点不就好了,最下面那一堆都是验证用的 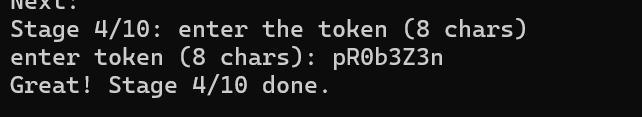 - - - - - - ### 阶段4->Stage5 (`sub_140117780`) **函数位置**:复杂的数据处理函数 从实际运行看,并不需要输入任何东西  - - - - - - ### 阶段5->Stage6(`sub_14011A330`) **函数位置**:生成文件 **功能**: 这个的主要功能就是检查你当前文件下是否有uvt\_crackme\_work\\stage2和stage2.sha256这两个文件,如果有测不在生成,如果没有则生成新的且在stage2中生成后续要用到的文件 **释放的文件**: - `E:\univsthreats26ctf\uvt_crackme_work\stage2\starfield_pings\pings.txt` - `E:\univsthreats26ctf\uvt_crackme_work\stage2\logs\system.log` - `E:\univsthreats26ctf\uvt_crackme_work\stage2\void\zen_void.bin` - 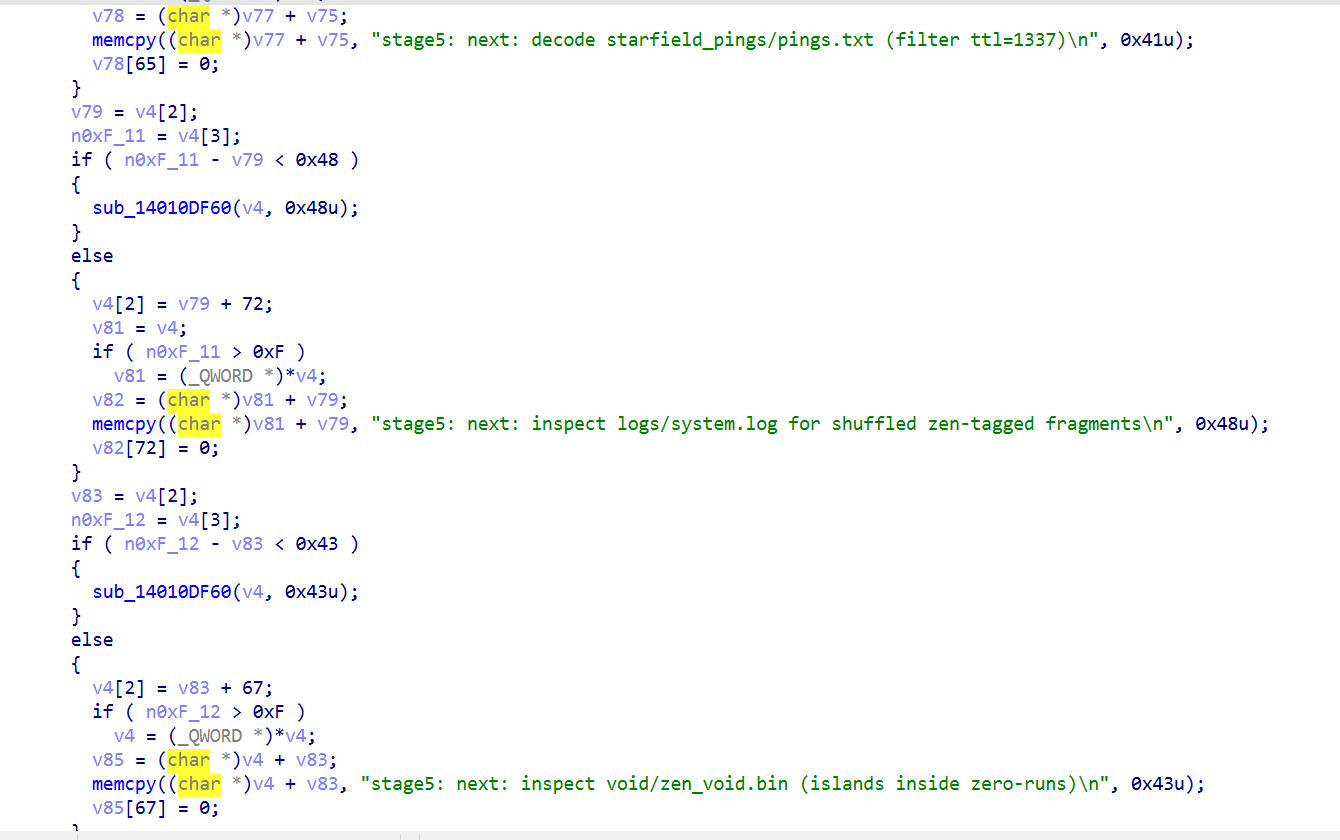 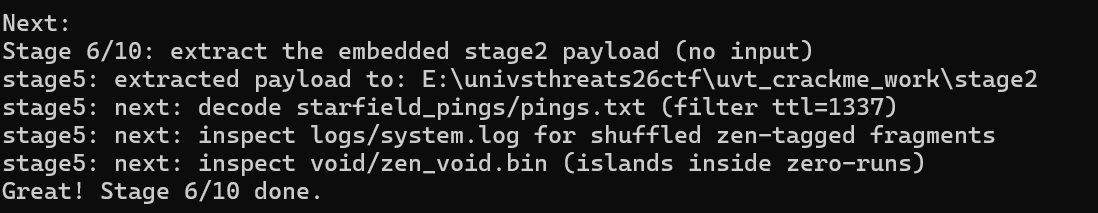 - - - - - - ### 阶段6->Stage7(`case 6 in main`) **函数位置**: 在main函数中的case 6中,这个并没有独立的函数 **关键代码**: 这里的关键代码在exe的提示词与pings.txt中 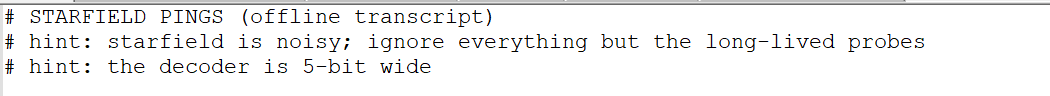 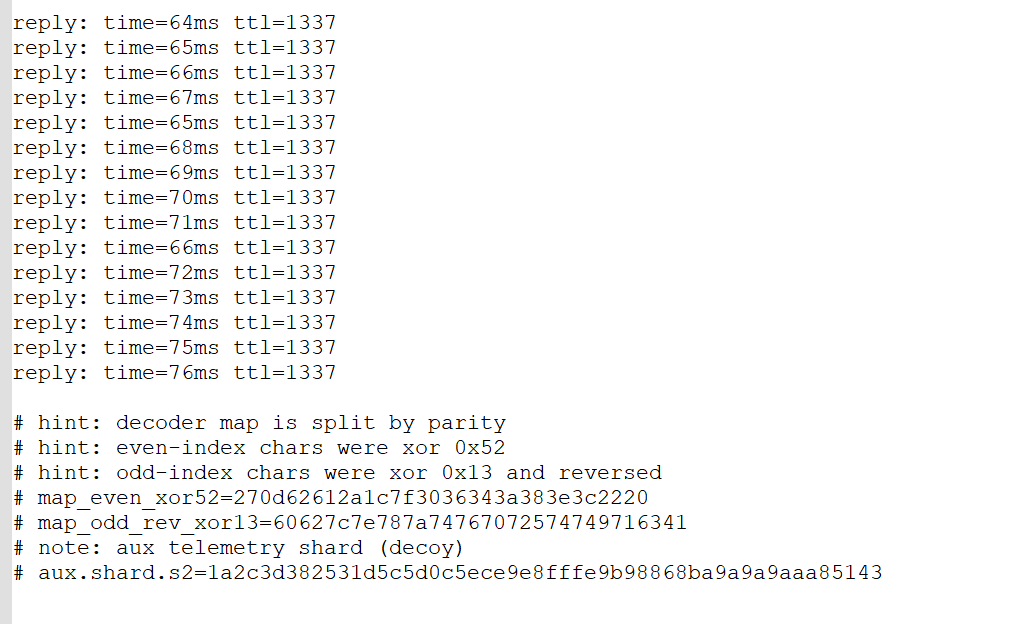  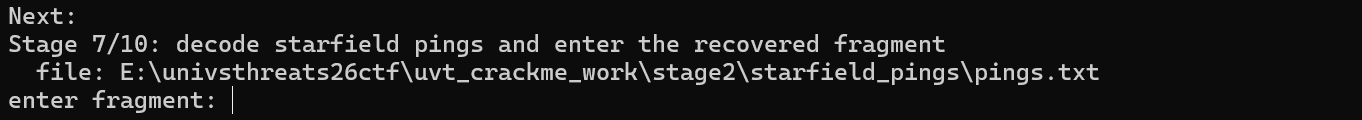 通过以上得知,从pings.txt中筛选`ttl=1337`的行,提取time的值: ```php reply: time=64ms ttl=1337 reply: time=65ms ttl=1337 reply: time=66ms ttl=1337 reply: time=67ms ttl=1337 reply: time=65ms ttl=1337 reply: time=68ms ttl=1337 reply: time=69ms ttl=1337 reply: time=70ms ttl=1337 reply: time=71ms ttl=1337 reply: time=66ms ttl=1337 reply: time=72ms ttl=1337 reply: time=73ms ttl=1337 reply: time=74ms ttl=1337 reply: time=75ms ttl=1337 reply: time=76ms ttl=1337 ``` 提取time值:`[64, 65, 66, 67, 65, 68, 69, 70, 71, 66, 72, 73, 74, 75, 76]` 然后又说要取低5位(time &0x1F)得到索引序列 `[0, 1, 2, 3, 1, 4, 5, 6, 7, 2, 8, 9, 10, 11, 12]` 最后在txt中给了两个映射表(偶索引异或0x52,奇索引异或0x13并反转)得到原始字节序列 然后编写一下脚本即可得到stage7的片段 ```php import re # 从 pings.txt 提取 ttl=1337 的 time 值 times = [] with open("uvt_crackme_work/stage2/starfield_pings/pings.txt") as f: for line in f: if "ttl=1337" in line: m = re.search(r"time=(\d+)", line) if m: times.append(int(m.group(1))) # 取低5位得到索引序列 indices = [t & 0x1F for t in times] # 得到 [0,1,2,3,1,4,5,6,7,2,8,9,10,11,12] # 映射表(十六进制字符串) even_hex = "270d62612a1c7f3036343a383e3c2220" odd_hex = "60627c7e787a74767072574749716341" even_bytes = bytes.fromhex(even_hex) odd_bytes = bytes.fromhex(odd_hex) result = [] for idx in indices: if idx % 2 == 0: # 偶数索引 pos = idx // 2 val = even_bytes[pos] ^ 0x52 else: # 奇数索引 pos = 15 - (idx // 2) # 反转后取 val = odd_bytes[pos] ^ 0x13 result.append(chr(val)) fragment = ''.join(result) print(f"Stage 7 fragment: {fragment}") # 输出: uR_pR0b3Z_xTND- ``` 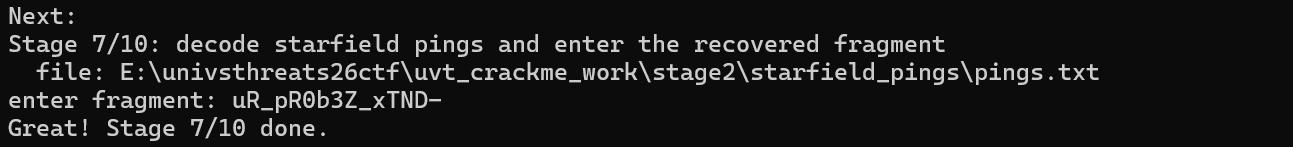 ### 阶段7->Stage8(`case 7 in main`) **函数位置**: 同样没有独立函数,在mian函数中的case7中 **关键代码**: 这里的关键代码在exe的提示词与logs目录下的README\_LOGS.txt中  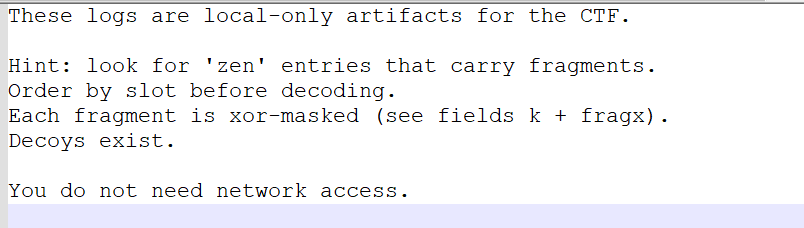 **关键逻辑**: 从提示中可以发现分析system.log中`subsys=“zen”`的条目带有`slot`、`t`、`fragx`字段,按照`slot`排序后,用`k`(十六机制)作为秘钥对`fragx`(十六进制字符串)进行异或,得到三个Base64片段,拼接解码即可获得Stage8的片段 #### 解码过程详解 **slot 1:** `k = "28"` → 0x28 fragx = `"7b7e1147657d79"` → 7字节: `7B 7E 11 47 65 7D 79` 异或后: `53 56 39 6F 4D 55 51` → `"SV9oMUQ"` **slot 2:** `k = "2f"` → 0x2F fragx = `"55771d435a771d"` → 7字节: `55 77 1D 43 5A 77 1D` 异或后: `7A 58 32 6C 75 58 32` → `"zX2luX2"` **slot 3:** `k = "36"` → 0x36 fragx = `"414164054650"` → 6字节: `41 41 64 05 46 50` 异或后: `77 77 52 33 70 66` → `"wwR3pf"` 拼接得到:`"SV9oMUQzX2luX2wwR3pf"` Base64 解码后:`"I_h1D3_in_l0Gz_"` #### 解密脚本 ```php import base64 import json # 从 system.log 提取 zen 条目 entries = [] with open("uvt_crackme_work/stage2/logs/system.log") as f: for line in f: if '"subsys":"zen"' in line: data = json.loads(line) slot = data["slot"] k = data["k"] fragx = data["fragx"] entries.append((slot, k, fragx)) # 按 slot 排序 entries.sort() result_b64 = "" for slot, k, fragx in entries: key = int(k, 16) frag_bytes = bytes.fromhex(fragx) xored = bytes(b ^ key for b in frag_bytes).decode() result_b64 += xored # result_b64 = "SV9oMUQzX2luX2wwR3pf" decoded = base64.b64decode(result_b64).decode() print(f"Stage 8 fragment: {decoded}") # 输出: I_h1D3_in_l0Gz_ ``` 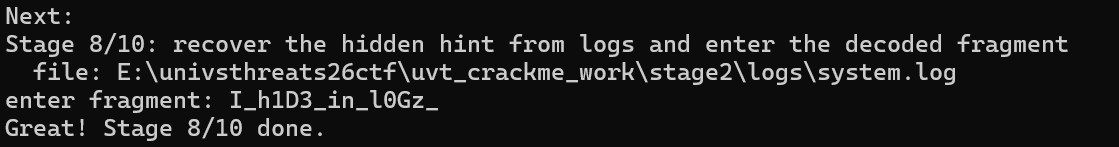 ### 阶段8->Stage9(`case 8 in main`) **函数位置**: 同样没有独立函数,在mian函数中的case8中 **关键代码**: 这里的关键代码在exe的提示词与void目录下zen\_void\_readme.txt的中  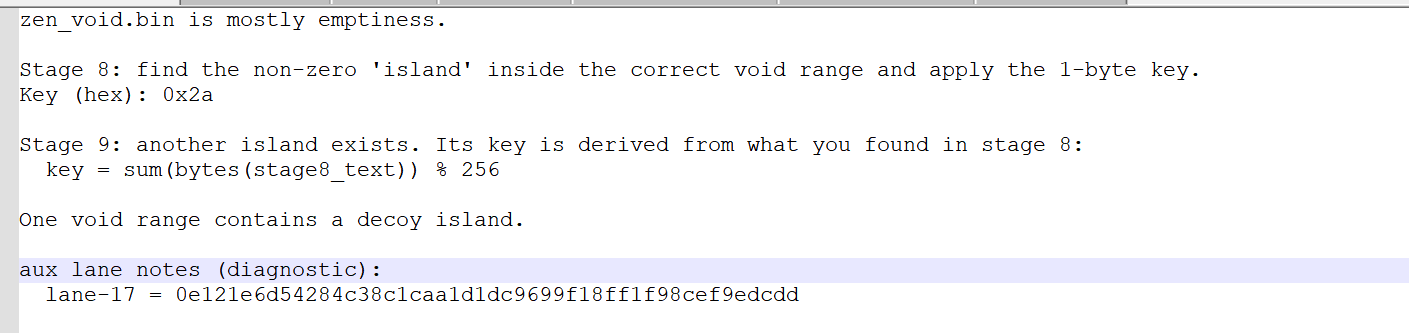 根据生成文件中给出的工具来提取zen\_void.bin中我们所需要的数据 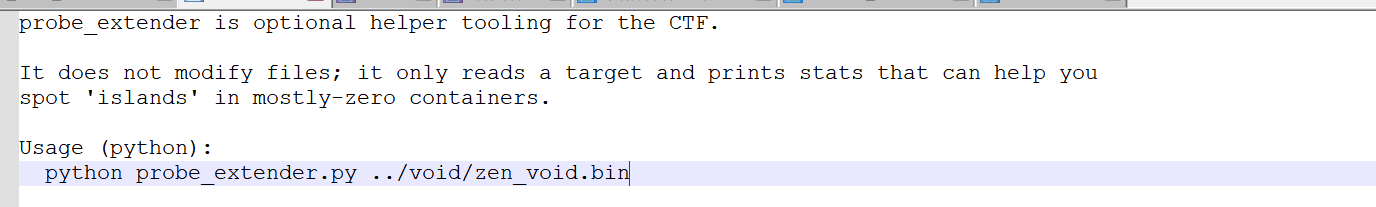 **辅助工具(**`**probe_extender.py**`**)** ```php #!/usr/bin/env python3 from __future__ import annotations import math import sys from pathlib import Path def shannon_entropy(b: bytes) -> float: if not b: return 0.0 counts = [0] * 256 for x in b: counts[x] += 1 n = len(b) ent = 0.0 for c in counts: if c == 0: continue p = c / n ent -= p * math.log2(p) return ent def find_islands(data: bytes, min_len: int = 4) -> list[tuple[int, int]]: out: list[tuple[int, int]] = [] i = 0 n = len(data) while i < n: if data[i] == 0: i += 1 continue j = i while j < n and data[j] != 0: j += 1 if j - i >= min_len: out.append((i, j - i)) i = j return out def main() -> None: if len(sys.argv) != 2: print(f"usage: {Path(sys.argv[0]).name} <file>") raise SystemExit(2) p = Path(sys.argv[1]) data = p.read_bytes() print(f"file: {p} ({len(data)} bytes)") islands = find_islands(data) if not islands: print("no non-zero islands found") return print(f"islands: {len(islands)}") for off, ln in islands[:32]: b = data[off : off + ln] ent = shannon_entropy(b) sample = b[:16].hex() print(f" off=0x{off:08x} len={ln:5d} entropy={ent:0.2f} sample={sample}") if __name__ == "__main__": main() ``` 运行脚本就可以得到我们所需要的数据 ```php file: ..\void\zen_void.bin (131072 bytes) islands: 7 off=0x00000000 len= 169 entropy=4.59 sample=5a454e564f494476310a74776f206361 off=0x00002345 len= 7 entropy=2.81 sample=13374445434f59 off=0x0000234d len= 4 entropy=2.00 sample=01020304 off=0x00009550 len= 8 entropy=2.75 sample=1d44755c1a1b6e75 off=0x00009d20 len= 8 entropy=3.00 sample=1136273e39313405 off=0x0000a1b2 len= 8 entropy=2.50 sample=1b44755c1a1b6e75 off=0x0000e3c4 len= 7 entropy=2.52 sample=113627223d3605 ``` **关键逻辑**: 提示中给出来stage9的key就是 `sum(bytes(stage8_text)) % 256`,最后计算发现key和给出来的一样都是`0x2a`,通过key与给出的数据进行异或,可以发现偏移`0x9550`与`0xa1b2`的样本只有一个字母不同也就是说这俩有一个真一个假 通过脚本来分析即可,最后发现`0xa1b2`这一组是我们需要的数据 **解密脚本**: ```php sample9 = "1b44755c1a1b6e75" key9 = 0x2a # 将十六进制字符串转换为字节 encrypted9 = bytes.fromhex(sample9) # encrypted9 = [0x1b, 0x44, 0x75, 0x5c, 0x1a, 0x1b, 0x6e, 0x75] # 异或解密 decrypted9 = bytes(b ^ key9 for b in encrypted9) # 计算过程: # 0x1b ^ 0x2a = 0x31 -> '1' # 0x44 ^ 0x2a = 0x6e -> 'n' # 0x75 ^ 0x2a = 0x5f -> '_' # 0x5c ^ 0x2a = 0x76 -> 'v' # 0x1a ^ 0x2a = 0x30 -> '0' # 0x1b ^ 0x2a = 0x31 -> '1' # 0x6e ^ 0x2a = 0x44 -> 'D' # 0x75 ^ 0x2a = 0x5f -> '_' stage9 = decrypted9.decode('ascii') # "1n_v01D_" print(f"Stage 9 fragment: {stage9}") # 输出: 1n_v01D_ ``` 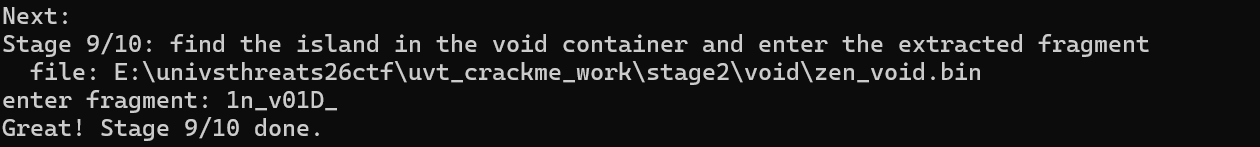 ### 阶段9->Stage10(`case 9 in main`) **函数位置**: 同样没有独立函数,在mian函数中的case9中 **关键代码**: 这里的关键代码在exe的提示词与void目录下zen\_void\_readme.txt的中 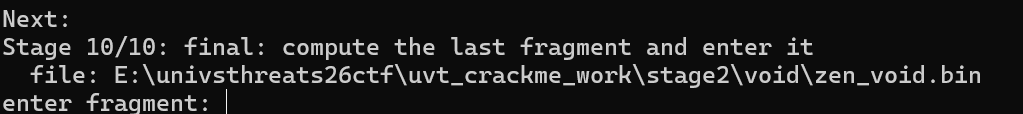 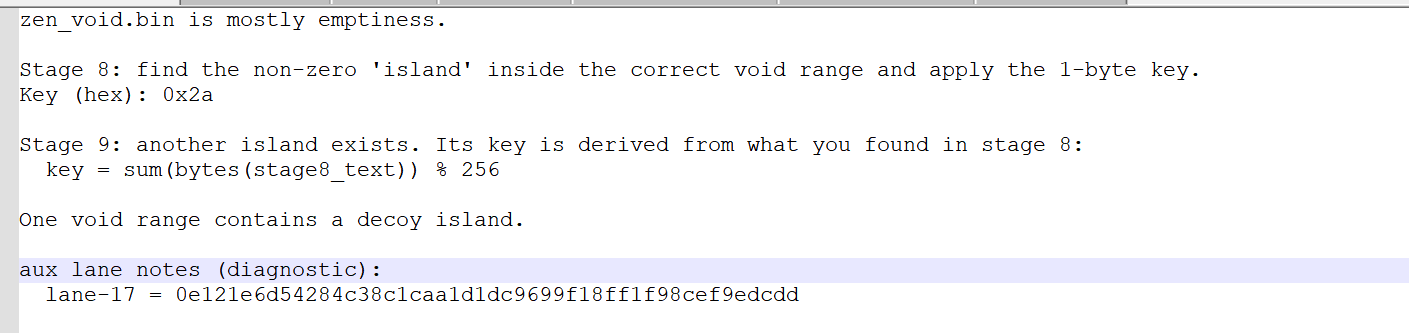 **关键逻辑**: 可以想一下,如果按照stage9的key计算那也可以计算出来stage10的key ```php stage9 = "1n_v01D_" key10 = sum(ord(c) for c in stage9) % 256 # 计算过程: # ord('1')=49, ord('n')=110, ord('_')=95, ord('v')=118, # ord('0')=48, ord('1')=49, ord('D')=68, ord('_')=95 # 总和 = 49+110+95+118+48+49+68+95 = 632 # 632 % 256 = 120 (0x78) print(f"Stage 10 密钥: 0x{key10:02x}") # 输出: 0x78 ``` 然后还是从刚才的数据中找岛,就会发现有两组又是很相似的样本:`0x9d20`和`0xe3c4` ```php file: ..\void\zen_void.bin (131072 bytes) islands: 7 off=0x00000000 len= 169 entropy=4.59 sample=5a454e564f494476310a74776f206361 off=0x00002345 len= 7 entropy=2.81 sample=13374445434f59 off=0x0000234d len= 4 entropy=2.00 sample=01020304 off=0x00009550 len= 8 entropy=2.75 sample=1d44755c1a1b6e75 off=0x00009d20 len= 8 entropy=3.00 sample=1136273e39313405 off=0x0000a1b2 len= 8 entropy=2.50 sample=1b44755c1a1b6e75 off=0x0000e3c4 len= 7 entropy=2.52 sample=113627223d3605 ``` 同样还是去异或,然后跑数据就会发现0`xe3c4`是我们最后要找的样本 **解密脚本**: ```php sample10 = "113627223d3605" key10 = 0x78 # 将十六进制字符串转换为字节 encrypted10 = bytes.fromhex(sample10) # encrypted10 = [0x11, 0x36, 0x27, 0x22, 0x3d, 0x36, 0x05] # 异或解密 decrypted10 = bytes(b ^ key10 for b in encrypted10) # 计算过程: # 0x11 ^ 0x78 = 0x69 -> 'i' # 0x36 ^ 0x78 = 0x4e -> 'N' # 0x27 ^ 0x78 = 0x5f -> '_' # 0x22 ^ 0x78 = 0x5a -> 'Z' # 0x3d ^ 0x78 = 0x45 -> 'E' # 0x36 ^ 0x78 = 0x4e -> 'N' # 0x05 ^ 0x78 = 0x7d -> '}' stage10 = decrypted10.decode('ascii') # "iN_ZEN}" print(f"Stage 10 fragment: {stage10}") # 输出: iN_ZEN} ``` 完整的flag ------- `UVT{Kr4cK_M3_N0w-cR4Km3_THEN-5T4rf13Ld_piNgS_uR_pR0b3Z_xTND-I_h1D3_in_l0Gz_1n_v01D_iN_ZEN}`
发表于 2026-03-23 09:00:02
阅读 ( 2448 )
分类:
二进制
0 推荐
收藏
0 条评论
Gscsed
1 篇文章
×
温馨提示
您当前没有「奇安信攻防社区」的账号,注册后可获取更多的使用权限。
×
温馨提示
您当前没有「奇安信攻防社区」的账号,注册后可获取更多的使用权限。
×
举报此文章
垃圾广告信息:
广告、推广、测试等内容
违规内容:
色情、暴力、血腥、敏感信息等内容
不友善内容:
人身攻击、挑衅辱骂、恶意行为
其他原因:
请补充说明
举报原因:
×
如果觉得我的文章对您有用,请随意打赏。你的支持将鼓励我继续创作!